Privacy conversations often focus on big obvious identifiers like email addresses, cookies, or GPS. The harder reality is that modern tracking can also be assembled from small pieces of runtime context. Battery behavior, canvas rendering, timing differences, viewport quirks, touch capability, font behavior, and hardware-linked hints can all become part of a larger fingerprint. One signal alone may look weak. A pile of them can become surprisingly persistent.
That is why browser fingerprinting keeps surviving after users do the things they think are enough. EFF’s Panopticlick work remains useful because it showed how high uniqueness can be even without a login. The point is not that every signal is equally important forever. The point is that many low-level details become more powerful when they are combined. A tracking system does not need perfect certainty to be useful. It only needs enough stability to group sessions, estimate confidence, and keep refining the profile.
Real-user measurement reinforces that this is not just a theoretical lab concern. A 2025 study based on actual user interactions reported that automated crawls missed almost half — 45% — of the fingerprinting websites users encountered in practice. That gap matters because it suggests many people experience more fingerprinting than standard measurement pipelines capture. Another 2025 study found robust evidence supporting the use of browser fingerprinting for ad tracking and targeting. The ecosystem still has incentives to keep these signals useful.
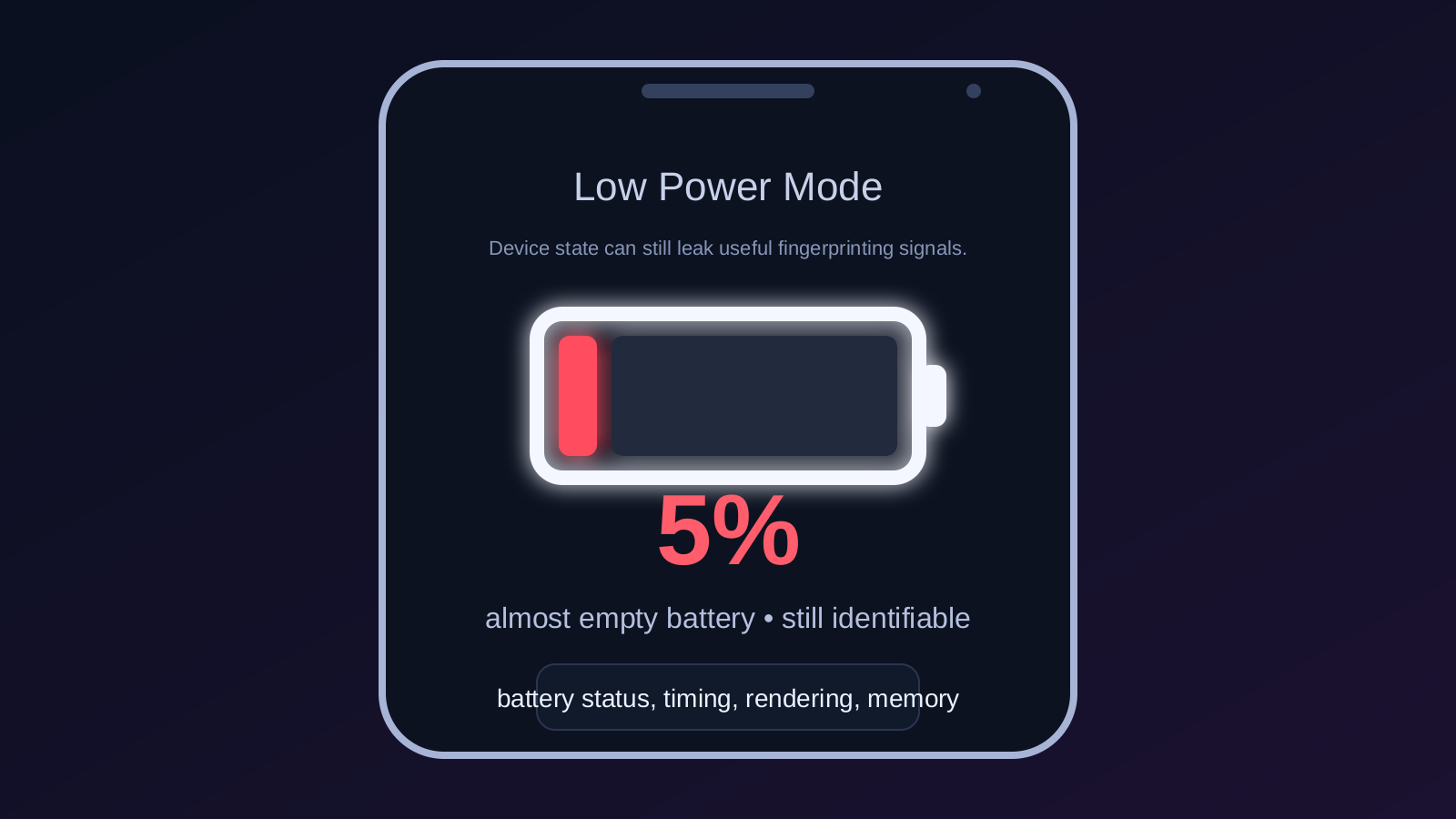
Battery status is a good example of the broader lesson. Over the years, some APIs have been restricted or deprecated because they leaked too much about device state. But the tracking problem did not vanish with any single change. Systems can keep rebuilding identity from adjacent signals: rendering behavior, performance timing, device memory hints, graphics stack details, and interaction patterns. Privacy products should not think in terms of one bad API. They should think in terms of how many weak signals are being assembled into a profile.
That is why Cloak should treat fingerprint reduction as an active defense layer, not a checkbox. The job is to weaken repeatable identity signals, explain when a session looks unusually fingerprint-heavy, and help the user understand that “I blocked cookies” is not the same thing as “I disappeared.” Small device signals still matter because platforms can still turn them into leverage.